CAN't
Adaptable Privacy for ISOBUS Controller Area Networks
Various components of modern agricultural machinery generate, transmit, and aggregate precise information about the environment. That data may contain sensitive information about a field's fertility, crop yields, and precise position information. This might be considered as unproblematic in traditional scenarios with a single farmer and farm-internal machinery. However, in todays agriculture, particularly in collaborative scenarios where multiple actors are involved in the value-added chain, it raises a variety of privacy issues.
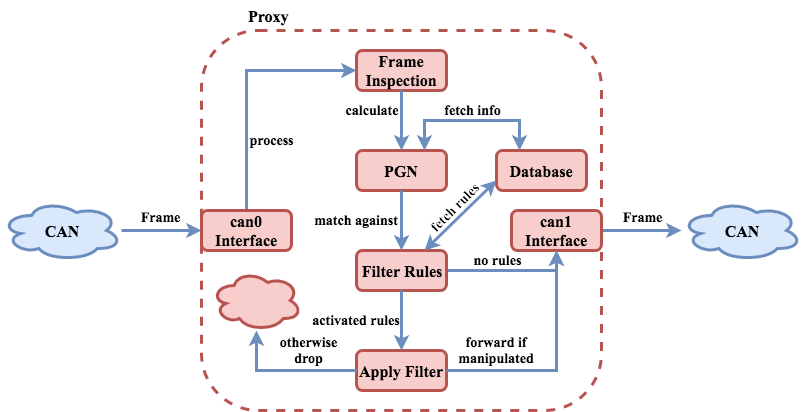
CAN't is a multithreaded proxy server software for
ISOBUS
Controller Area Networks.
By acting as man-in-the-middle between Electronic Control Units, it enables
selective, on-the-fly perturbation and filtering of privacy sensitive information transmitted via the in-vehicular network.
When the proxy is injected between a data-logging component and the rest of the network, it can be used to enforce
privacy guidelines and laws to protect contractors, staff members, and customers from excessive data aggregation.
The proxy can be configured using an HTML5-based webinterface and is easily extendable by custom data filters and
manipulators. Due to its lightweight memory- and CPU-footprint, it can run on cheap off-the-shelf hardware
(e.g., the Raspberry Pi 3), as long as the corresponding CAN-Controller is supported by
SocketCan.
Further information can be found under Publications.
CAN't was developed as part of a security architecture in the project ODiL and is available as open source software under the 3-Clause BSD License. The database can be seeded using the exported ISOBUS Parameters provided by the VDMA in CSV format. For download links, see below.
Questions, suggestions and bug reports may be sent to
CryptoCAN
Minimalistic and Robust CAN-Bus Encryption
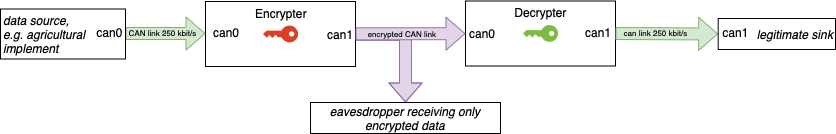
Especially in the agricultural sector, but not only there, the confidentiality of CANs is based solely on their physical inaccessibility. This may be true for many scenarios, but as soon as different devices of the actors are involved in a single bus, it becomes necessary to encrypt the transferred data. CryptoCAN is a set of tools for pluggable encryption under various conditions and use cases with respect to the bus-specific needs. All programs are designed to run on a Linux system using SocketCan, however their modular design makes it possible to port it with minimal effort to other platforms. CryptoCAN especially considers the impact of the encryption on the overall bus robustness and, therefore, enables encryption even for partially unreliable CANs with minimal influence on the bus load.
For ISOBUS networks CryptoCAN allows to partially encrypt confidential information within the data stream, while forwarding necessary control messages without encryption. For other upper layer protocols, which rely on the correct length of received frames, a solution utilizing unused bits in the CAN protocol is supplied. As all en- and decryption programs rely on a Linux system using SocketCAN, this encryption requires an adapted CAN-controller driver, which is exemplarily provided for the MCP2515 controller.
An integration with CAN't allows to enable or disable the encryption for specific ISOBUS PGNs in the existing GUI and, therefore, can be used as an example for the straightforward adaption to existing software projects.
CryptoCAN is available under the GPL v2 License.
Questions, suggestions and bug reports may be sent to
Publications
-
Jan Bauer, René Helmke, Alexander Bothe, Nils Aschenbruck
"CAN’t track us: Adaptable Privacy for ISOBUS Controller Area Networks"
Elsevier Computer Standards and Interfaces, 2019. [pdf] -
René Helmke, Jan Bauer, Alexander Bothe, Nils Aschenbruck
"CAN’t — An ISOBUS Privacy Proxy for Collaborative Smart Farming"
Poster Paper for the 38th IEEE International Performance Computing and Communications Conference
IPCCC, London, England, UK, Oct. 29-31, 2019. [pdf] -
Till Zimmermann, Jan Bauer, Nils Aschenbruck
"CryptoCAN — Ensuring Confidentiality in Controller Area Networks for Agriculture"
Proc. of the Jahrestagung des Fachbereichs "Sicherheit — Schutz und Zuverlässigkeit" der GI
SICHERHEIT 2020, Göttingen, Germany, Mar. 17-20, 2020. [pdf] -
Jan Bauer, René Helmke, Till Zimmermann, Alexander Bothe, Michel Löpmeier, Nils Aschenbruck
"Crypto CAN’t — Confidentiality and Privacy for CAN/ISOBUS Networks in Precision Agriculture"
Demo at the 44th IEEE Conference on Local Computer Networks
LCN, Osnabrück, Germany, Oct. 14-17, 2019. [pdf]
Downloads
- CAN't Version 1 (December 2018)
- CryptoCAN (Github)
- CAN't (Github) (incl. CryptoCAN integration)